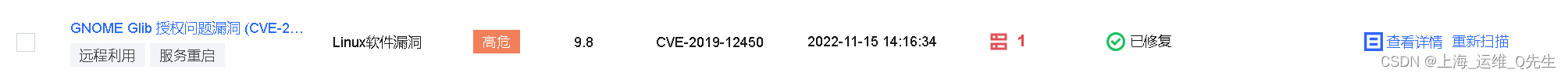
漏洞修复--GNU C Library 安全漏洞 (CVE-2020-29573) GNOME Glib 授权问题漏洞 (CVE-2019-12450)
漏洞 修复 -- 2019 2020 授权 CVE library
2023-09-14 09:02:05 时间
1. 漏洞描述:
GNUCLibrary(glibc,libc6)是一种按照LGPL许可协议发布的开源免费的C语言编译程序。GNUCLibrary2.23之前版本存在安全漏洞,该漏洞源于。如果任何printf函数族的输入是80位长的双精度数,且x86目标上的2.23之前的GNU C库(即glibc或libc6)中的sysdeps / i386 / ldbl2mpn.c在x86目标上具有基于堆栈的缓冲区溢出。
GNOMEGlib是一套用于创建图形用户界面的多平台工具包,是GTK+和GNOME工程的基础底层核心程序库。GNOMEGlib2.15.0版本至2.61.1版本中存在授权问题漏洞。该漏洞源于网络系统或产品中缺少身份验证措施或身份验证强度不足。
2. 解决方法
使用阿里云或者腾讯云的仓库,具体方法其他文章有说明
sudo yum update -y glibc-common glibc-headers glibc glibc-devel glib2
3. 修复过程
# sudo yum update -y glibc-common glibc-headers glibc glibc-devel glib2
Loaded plugins: fastestmirror, langpacks
Loading mirror speeds from cached hostfile
Resolving Dependencies
--> Running transaction check
---> Package glib2.x86_64 0:2.56.1-5.el7 will be updated
---> Package glib2.x86_64 0:2.56.1-9.el7_9 will be an update
---> Package glibc.x86_64 0:2.17-307.el7.1 will be updated
---> Package glibc.x86_64 0:2.17-326.el7_9 will be an update
---> Package glibc-common.x86_64 0:2.17-307.el7.1 will be updated
---> Package glibc-common.x86_64 0:2.17-326.el7_9 will be an update
---> Package glibc-devel.x86_64 0:2.17-307.el7.1 will be updated
---> Package glibc-devel.x86_64 0:2.17-326.el7_9 will be an update
---> Package glibc-headers.x86_64 0:2.17-307.el7.1 will be updated
---> Package glibc-headers.x86_64 0:2.17-326.el7_9 will be an update
--> Finished Dependency Resolution
Dependencies Resolved
===========================================================================================================================================================================
Package Arch Version Repository Size
===========================================================================================================================================================================
Updating:
glib2 x86_64 2.56.1-9.el7_9 updates 2.5 M
glibc x86_64 2.17-326.el7_9 updates 3.6 M
glibc-common x86_64 2.17-326.el7_9 updates 12 M
glibc-devel x86_64 2.17-326.el7_9 updates 1.1 M
glibc-headers x86_64 2.17-326.el7_9 updates 691 k
Transaction Summary
===========================================================================================================================================================================
Upgrade 5 Packages
Total download size: 19 M
Downloading packages:
Delta RPMs disabled because /usr/bin/applydeltarpm not installed.
(1/5): glibc-2.17-326.el7_9.x86_64.rpm | 3.6 MB 00:00:00
(2/5): glib2-2.56.1-9.el7_9.x86_64.rpm | 2.5 MB 00:00:00
(3/5): glibc-devel-2.17-326.el7_9.x86_64.rpm | 1.1 MB 00:00:00
(4/5): glibc-common-2.17-326.el7_9.x86_64.rpm | 12 MB 00:00:00
(5/5): glibc-headers-2.17-326.el7_9.x86_64.rpm | 691 kB 00:00:00
---------------------------------------------------------------------------------------------------------------------------------------------------------------------------
Total 14 MB/s | 19 MB 00:00:01
Running transaction check
Running transaction test
Transaction test succeeded
Running transaction
Updating : glibc-common-2.17-326.el7_9.x86_64 1/10
Updating : glibc-2.17-326.el7_9.x86_64 2/10
Updating : glibc-headers-2.17-326.el7_9.x86_64 3/10
Updating : glibc-devel-2.17-326.el7_9.x86_64 4/10
Updating : glib2-2.56.1-9.el7_9.x86_64 5/10
Cleanup : glibc-devel-2.17-307.el7.1.x86_64 6/10
Cleanup : glibc-headers-2.17-307.el7.1.x86_64 7/10
Cleanup : glib2-2.56.1-5.el7.x86_64 8/10
Cleanup : glibc-common-2.17-307.el7.1.x86_64 9/10
Cleanup : glibc-2.17-307.el7.1.x86_64 10/10
Verifying : glibc-headers-2.17-326.el7_9.x86_64 1/10
Verifying : glibc-2.17-326.el7_9.x86_64 2/10
Verifying : glib2-2.56.1-9.el7_9.x86_64 3/10
Verifying : glibc-devel-2.17-326.el7_9.x86_64 4/10
Verifying : glibc-common-2.17-326.el7_9.x86_64 5/10
Verifying : glibc-headers-2.17-307.el7.1.x86_64 6/10
Verifying : glib2-2.56.1-5.el7.x86_64 7/10
Verifying : glibc-devel-2.17-307.el7.1.x86_64 8/10
Verifying : glibc-common-2.17-307.el7.1.x86_64 9/10
Verifying : glibc-2.17-307.el7.1.x86_64 10/10
Updated:
glib2.x86_64 0:2.56.1-9.el7_9 glibc.x86_64 0:2.17-326.el7_9 glibc-common.x86_64 0:2.17-326.el7_9 glibc-devel.x86_64 0:2.17-326.el7_9
glibc-headers.x86_64 0:2.17-326.el7_9
Complete!
4. 重新扫描

相关文章
- fastjson漏洞复现
- 【漏洞复现】Apache HTTP Server 2.4.49、2.4.50 RCE(CVE-2021-41773)
- OpenSSL心脏滴血漏洞
- 任意密码重置漏洞(身份认证缺失)
- 【漏洞预警】Linux Kernel openvswitch 模块权限提升漏洞(CVE-2022-2639)POC复现及修复方法
- Web攻防作业 | 越权访问漏洞全解析
- 【公益译文】了解、预防、修复:开源漏洞讨论框架
- 【错误记录】Android 应用安全检测漏洞修复 ( StrandHogg 漏洞 | 设置 Activity 组件 android:taskAffinity=““ )
- Linux漏洞修复:拯救安全的必要武器(linux漏洞修复软件)
- MySQL安全性:防止漏洞攻击的必要措施(mysql漏洞)
- 开发者发现苹果自研M1有巨大漏洞:不改设计无法修复
- 微软为已停止支持的Exchange服务器提供补丁 修复近期重大漏洞
- Win10迎来六月累积更新:修复49个漏洞
- 英特尔修复一个它六个月前就声称已修复的漏洞
- 黑客正在利用多个 WordPress 插件的 0day 漏洞对网站发起攻击
- Linux Mint 修复了两个孩子发现的屏保锁定绕过漏洞
- 再探Stagefright漏洞——POC与EXP
- Discuz!X前台任意文件删除漏洞重现及分析
- “优雅”的Linux漏洞:用罕见方式绕过ASLR和DEP保护机制
- 码农代码审计:php漏洞
- 360承认儿童安全卫士存在漏洞,感谢GeekPwn
- Redis安全漏洞:未经授权访问。(redis未授权访问漏洞)
- Oracle漏洞修复:一款安全的保障(oracle漏洞修复工具)
- Oracle10漏洞修复快步前进(oracle10漏洞修复)
- 已修复漏洞仍导致6万网站被黑;美女黑客被无故扣污名 | 宅客周刊
- Linux用户要注意修复漏洞

