[AWS] Talk: Getting started with AWS identity
IAM roles for non-human access
Any application you wrote in the cloud is probably going to accessing some other resources ion the cloud like, EC2 instance and Lambda functions need to access S3 or DynamoDB.
You need some identity to make those API calls to access data. Those API calls and that identity would be an IAM role.
So that you, as a developer doesn't need to handle any credentials at all, you just associate a role with this instance or with this lambda function. AWS will take care to rotate those credentials.

In Management Console, you will see:
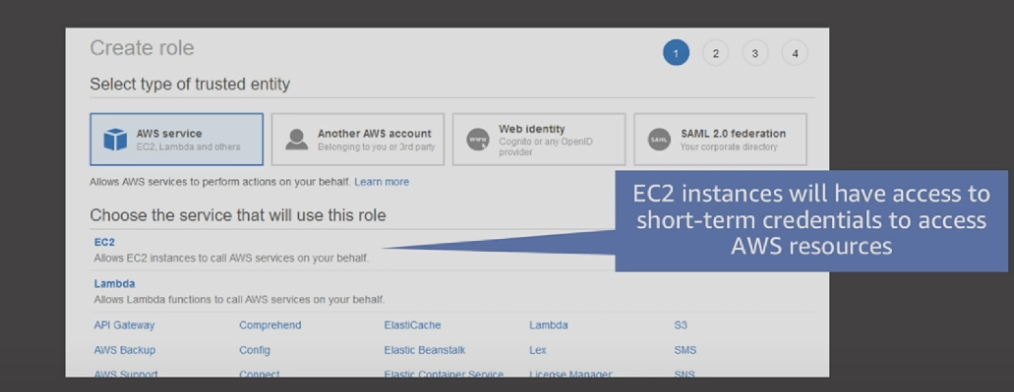
"AWS Service" & "Another AWS account", first one is non-human access, second one is human-access.
Some questions like:
A developer is running an application on an Amazon EC2 instance that requires access to an Amazon S3 bucket. An administrator creates a role that includes policies that grant read permissions to the bucket and that allow the developer to launch the role with an Amazon EC2 instance. The instance is launched with the created role attached. What additional step is required for the application running on the instance to access the objects in the bucket?
"EC2 instance has role to access S3", which means non-human access IAM role is assoicated. So it is enough for EC2 instance to access objects inside that bucket.
Answer selection:
A. Create an IAM policy that allows the developer permissions to access the bucket.
Attach the policy to the developer's IAM User.
B. No other steps are necessary. The application running on the instance
will be able to access the bucket.
C. The administrator must grant the developer permissions to access the bucket.
A: Try to confuse you, whether you still need to give human-access to S3, NOT necessary if developer himself not going to access S3. Only EC2 instance need to access S3.
B: Which is correct
C: The same as A.

Because you may have some user just need to read data other than modify data, always give a "ReadOnly" role makes life easier.
IAM resource in JSON
The place to find which actions you can allow in the resource.
Example:

Question: To save cost, you only want some cheap instance to be launched. So add "Condition", only allow "t3.nano/micro".
Chose options is correct?



Answer: C
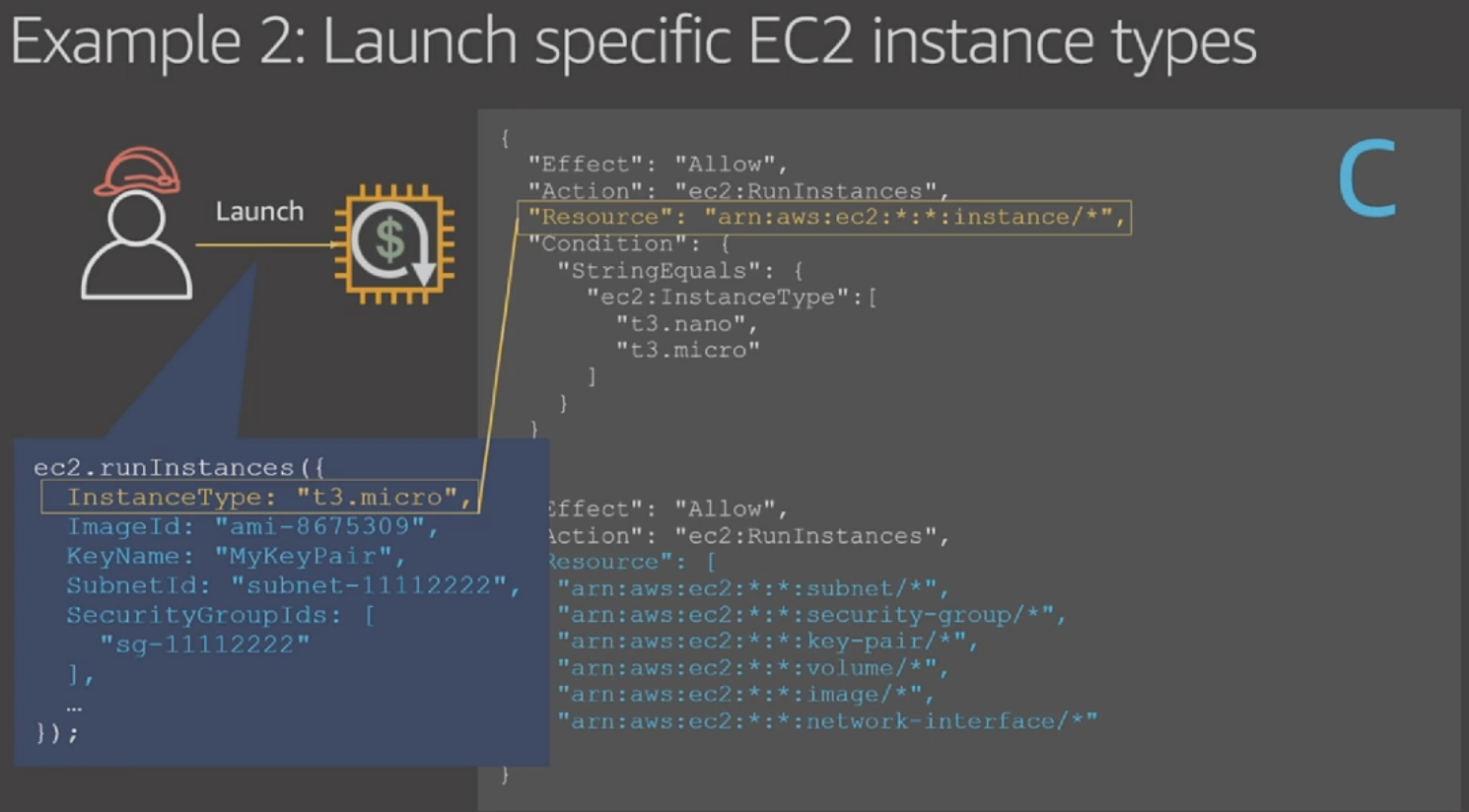
When IAM doing the permission matching.
For example: "security-group", it doesn't have "InstanceType" attr, therefore, it results in an deny condiiton.
Resource based policy
One account wants to access the S3 bucket in another account.
We can use "Principal" section for S3 policy, in "Principal", list the AWS account ID which are allowed.
In acount 111xx, also need to list S3 bucket into "Resource"

Multi accounts want to access S3 bucket
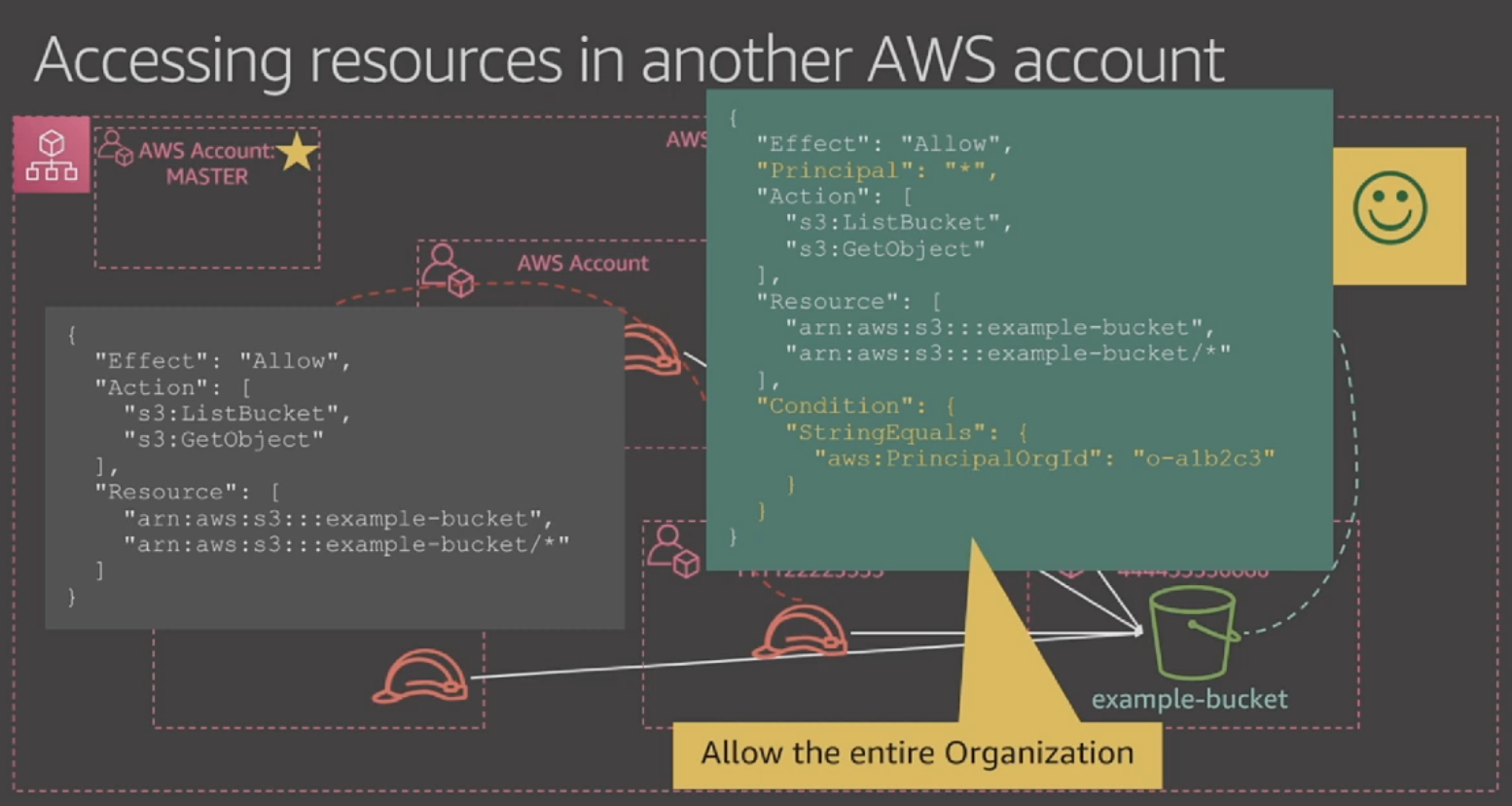
Using "PrincipalOrgId".
Assume Role for cross acount access


In DyanmoDB Table, add "Action": "sts:AssumeRole" and "Princiapal" for the AWS account wants to access this table.
For the account want to access Table, add "Action": "sts:AssumeRole" as well.

相关文章
- [工作随笔]Python 和AWS CDK的aws-route53那些事
- 亚马逊AWS自研芯片深度分析
- AMD专访:收购Pensando不是为了AWS,但是Chiplet可以搞起来
- MySQL Error number: MY-011415; Symbol: ER_KEYRING_AWS_FAILED_TO_SET_CMK_ID; SQLSTATE: HY000 报错 故障修复 远程处理
- MySQL Error number: MY-013485; Symbol: ER_KEYRING_AWS_INCORRECT_PROXY; SQLSTATE: HY000 报错 故障修复 远程处理
- AWS主要服务详解架构师
- 亚马逊最赚钱AWS业务添三大AI工具,这里是亮点和售价一览表
- AWS宣布3款实例进军中国市场,基于自研服务器芯片Graviton2,强化在华云策略
- 亚马逊AWS机器学习总监Alex Smola:如何用MXNet构建可拓展的深度学习框架?|AAAI 2017
- 数据库使用AWS连接本地MySQL数据库(aws调用本地mysql)
- 深入研究AWS如何调用MySQL(aws调用mysql)
- AWS改变MySQL配置,创建更加美好的未来(aws改mysql配置)
- AWS搜索 进入MySQL引擎的新时代(aws搜索MySQL引擎)
- 使用AWS管理MySQL,了解相关费用支出(aws mysql 费用)
- 实现高可用性的AWS与MySQL复制(aws mysql 复制)
- 利用AWS拉取MySQL日志,轻松掌控数据安全(aws拉取mysql日志)
- 分析学习Oracle深入理解使用With 分析(oracle使用with)
- Oracle中利用WITH子句的使用(oracle中的with)
- 语句使用Oracle两个WITH语句实现数据查询(oracle两个with)

